There's a pattern in how movements use technology. At first, technology facilitates inspiration: the phone call, the group chat, the social post, the encrypted Signal thread that births the initial campaign concept. Then comes coordination: the shared planning doc, the spreadsheet of contacts, the calendar of actions. And next, if the movement grows long enough, comes the painful realization that these technologies were never designed to work together, were never designed for an activist purpose at all, and that the gaps between them are where movements fail, dissipating while overwhelmed organizers burn out trying to hold it all in their heads.
I've spent the last year building Outcry as a thinking tool. An AI that could meet organizers where they are. The result is an Activist AI that is exceptionally good at talking to experienced, late-stage activists and organizers who don't want easy answers. Today, Outcry is having the kind of extended strategic conversation that most organizers can't find in their daily life... answering complex interdisciplinary questions that I'd struggle to grasp. The premise of the importance of an activist AI hasn't changed. If anything, watching people return to Outcry each day has deepened our conviction that cognitive infrastructure for activists is a real and underserved need.
But something else became clear. The organizers who got the most from Outcry kept bumping into the same wall: they'd have a breakthrough insight in conversation, then have to leave to coordinate action somewhere else entirely. The thinking happened with Outcry. The doing happened in a dozen fragmented corporate tools, most of them built by companies that hand over user data. The gap between strategic intelligence and operational security wasn't just inconvenient. For people doing high-risk work, it was dangerous.
So, emboldened by the rise of AI agents, I asked a question that turned out to be more ambitious than I expected: what if the activist thinking tool was also the activist doing tool? What if the Outcry that helps you analyze a campaign also lives on a computer you control: persistent, encrypted, networked to your collaborators, and capable of executing on what you decide?
The next Outcry is an operating system.
This Activist Operating System is not metaphorical. It is the next iteration of Outcry… OutcryOS.
Here's how it works:
Each user gets a persistent encrypted computer in the cloud. It doesn't disappear when you close your browser. Your files, your notes, your contacts, your communication history live on, encrypted at rest using envelope encryption with AWS KMS and gocryptfs FUSE filesystems. When an OutcryOS is created, KMS generates a data encryption key inside a FIPS 140-2 Level 3 hardware security module—hardware designed to show evidence of physical tampering and zeroize keys if tampered with. The plaintext key encrypts the user's filesystem via gocryptfs, then is zeroed from memory. What's stored in our database is the ciphertext version of that key, which is useless without the HSM. When OutcryOS sleeps, the plaintext key exists nowhere—not on disk, not in any database, not in any persistent storage. Recovering it requires a call to KMS with valid IAM credentials scoped to a single key alias. The security properties are identical to what banks use for data at rest.
Outcry runs on this machine, with access to an activist knowledge base of thousands of activist books and zines organized across radical theory, protest tactics, movement case studies, and strategic literature. When the AI performs a keyword search for historical precedent, it's searching an index that lives on your encrypted cloud computer using ripgrep—no external service involved. Semantic search is more nuanced: the FAISS vector index runs locally on each OutcryOS, but generating the query embedding currently requires a call to an external AI provider, relayed through our servers. The index lookup is local and private. The query vectorization step is not. Keyword searches via ripgrep are fully private end to end.
But compute without connectivity is just a bunker. And organizers don't work alone.
Every OutcryOS connects to every other OutcryOS through a WireGuard-encrypted mesh network built on Tailscale. When two OutcryOS machines are online simultaneously, Tailscale establishes direct WireGuard tunnels between them: peer-to-peer, with no intermediary. When direct connections fail, traffic falls back to a peer relay we self-host on our own infrastructure. In both cases, WireGuard encryption means the transport layer sees only scrambled ciphertext. The mesh strengthens as more people join it. Each new OutcryOS is another node in the network.
OutcryOS has a built-in knowledge base of thousands of activist texts spanning hundreds of authors, decades of case studies, hundreds of zines and organizing guides embedded into semantic vectors and indexed. The resulting FAISS index—5.4 gigabytes, IndexIVFFlat with inner product similarity over 3,072-dimensional vectors—runs locally on each OutcryOS alongside ripgrep for keyword search.
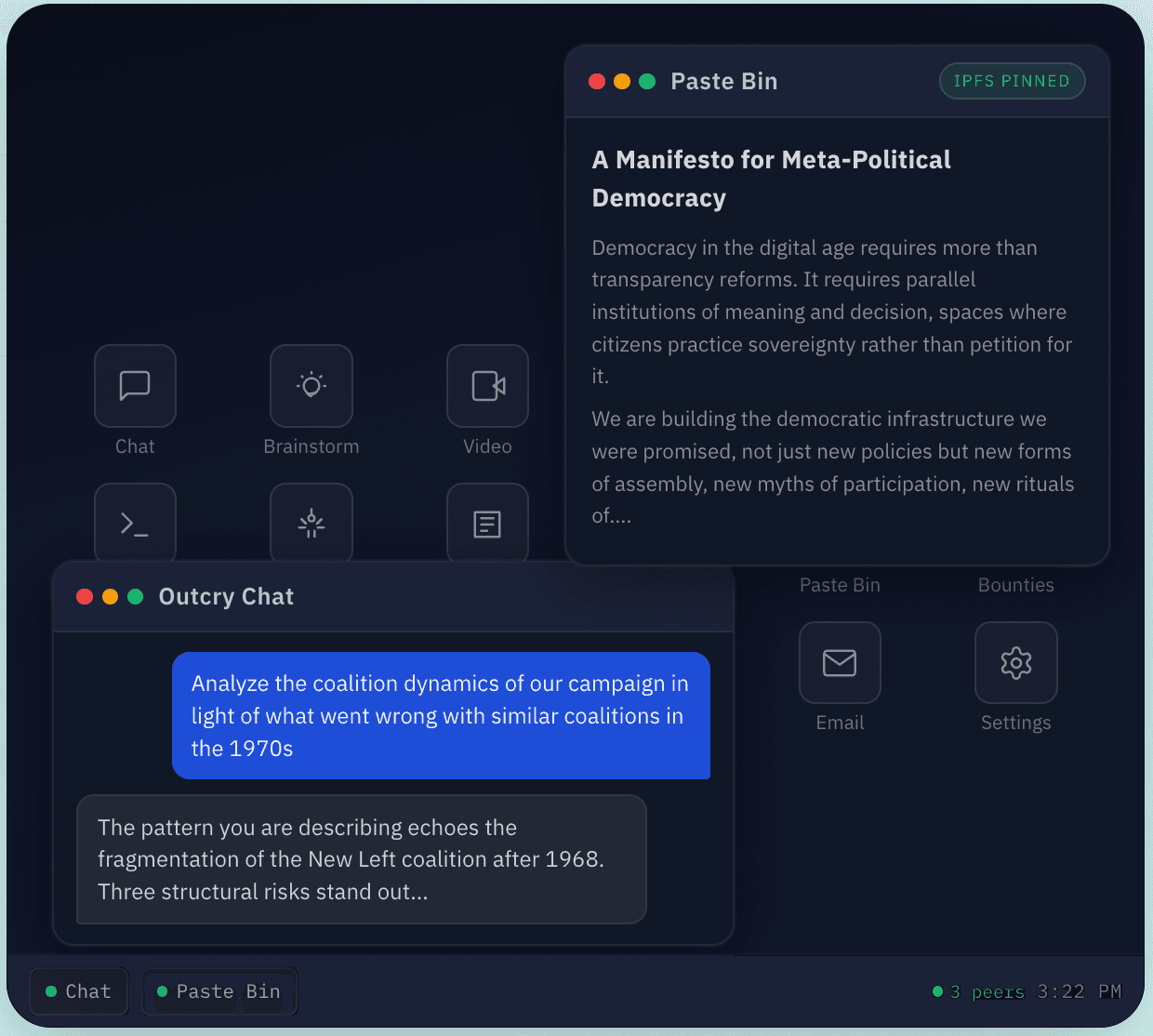
What can you actually do on this thing? The goal is an Activist OS with useful applications for organizers anyone can add. To start, we'll ship OutcryOS with the basics. A collaborative document editor built on CRDTs, so two organizers can co-edit a strategy document with conflicts resolved automatically, plus edits made offline merge cleanly when connectivity returns. A contacts system designed for the particular needs of movement work: relationship management by codename, affinity groups, trust designations, the social graph of a campaign without exposing anyone's legal identity. A media vault for organizing visual evidence and documentation. An encrypted pastebin with optional IPFS pinning, so you can publish something from within the OS that's resistant to takedown. A canary (a dead man's switch that auto-notifies your contacts and can wipe your files if you don't check in) because some of the people who need this tool operate in environments where that feature isn't paranoia but planning.
And underneath all of it is Outcry's evolution into an autonomous agent. Not a separate app you switch to. Outcry has control of your encrypted machine in the cloud, with access to the full knowledge base and the ability to execute shell commands on your behalf. Ask it to draft a press strategy drawing on historical examples of media campaigns during labor disputes, and it searches the theory, surfaces relevant case studies, and writes the document to your encrypted filesystem. Ask it to analyze the coalition dynamics of your campaign in light of what went wrong with similar coalitions in the 1970s, and it pulls from the tactical literature while you think out loud. It's not a chatbot bolted onto a dashboard. It's a shell: the command line of an operating system that treats strategic intelligence as a first-class capability.
I want to be honest about what this is and what it isn't. It's infrastructure. It's not a movement in-itself. It doesn't replace the irreducibly human work of strategy, courage, and solidarity. I'm building OutcryOS because I believe the people doing the most important democracy work in the world deserve infrastructure that enables their strategic creativity while matching the seriousness of what they're attempting.
There's a question that any project like this has to answer honestly: who controls it? I chose an architecture where the answer is as close to "you" as current technology allows. Your encryption keys are generated server-side by AWS KMS hardware security modules: born inside tamper-resistant hardware and the plaintext never touches persistent storage. Your data lives on your encrypted cloud computer, not in our application database. The mesh network connects your machine directly to your collaborators' machines via WireGuard. We're building toward a platform, not just a product, because platforms create the conditions for movements to build what they need.
For those who fund movements: the question isn't just whether your grantees have secure communications. It's whether they have secure infrastructure: compute, storage, AI, coordination tools that work together under their control. Communication is one layer. An activist operating system is all of them.
For those who build for movements: the Outcry API remains the fastest way to add organizing intelligence to any application. Easy to integrate, pay-as-you-go, designed for movement budgets. But if what you need isn't an API call but a secure environment, a place where the AI and the tools and the encrypted infrastructure are unified, then the OutcryOS is what we've been building toward all along.
Activists know the loneliness of sophisticated strategic thinking with no one to think alongside. We built this for you. Not to replace your judgment, but to give it a place to live: persistent, encrypted, connected, and yours.
The Hardest Problem We Haven't Solved
Everything described above has a dependency that should trouble anyone who thinks seriously about activist infrastructure: the AI itself runs on someone else's computers.
Outcry's intelligence comes from large language models accessed via API, currently from providers like OpenAI, Anthropic and Google. For OutcryOS, we've built extensive privacy architecture around the edges: your knowledge base searches happen locally, your files are encrypted at rest with keys you control, your mesh traffic is WireGuard-encrypted end to end. But when you ask OutcryAI a question, the conversation itself, your strategic thinking, your campaign analysis, your most sensitive hypotheticals, travels to a model provider's servers, is processed in their infrastructure, and is subject to their data policies, their compliance obligations, and their government's legal jurisdiction.
This isn't a secret. It's the fundamental constraint of AI in 2026. The models capable of the kind of nuanced strategic reasoning that makes Outcry useful, models that can engage with complex coalition dynamics, synthesize across decades of tactical literature, and respond in real time, exist only as proprietary APIs run by a handful of corporations. There is no state-of-the-art language model that an activist organization can run on its own servers today. Not at the quality level that makes the tool worth using.
We see two paths forward, and we think the honest answer is that both are necessary.
Path One: Privacy-Enhanced Cloud AI
On this path, we continue using frontier models from Anthropic, OpenAI, and others, but implement aggressive privacy measures around the interaction. Techniques like co-mingling user conversations so that no single session can be attributed to an individual. Request routing that strips identifying metadata before it reaches the model provider. Differential privacy approaches that add noise to queries. Contractual and technical controls that limit what providers can retain or train on. This path preserves what makes Outcry useful today: fast inference, real-time conversation, the ability to think alongside an AI that responds with sophistication. The tradeoff is that some trust in the model provider remains irreducible. You can minimize what they see and what they can do with it. You cannot eliminate the fact that your words pass through their systems.
Path Two: Private Activist AI.
On this path, open-source language models (DeepSeek, Qwen, Kimi and others) are approaching the capability threshold where they could serve as the reasoning engine for a tool like Outcry. It is technically possible to fine-tune an open-source model on activist literature and run it inside a Trusted Execution Environment (TEE): encrypted hardware enclaves where even the server operator cannot inspect the computation. This would mean that an activist's conversation with AI never exists in plaintext outside of tamper-resistant hardware. The model provider is eliminated entirely. Your strategic thinking stays inside infrastructure that is cryptographically verified to be running the code it claims to be running.
The obstacle is cost and capability. Running a model large enough to be genuinely useful requires GPU infrastructure that costs thousands of dollars per month to keep online. For an activist tool with a small user base, that's prohibitive. The realistic version of private activist AI looks less like a chatbot and more like an asynchronous advisor: servers that sleep when idle, take a minute or more to wake up and respond, and interact with you over email or Signal rather than in a live chat interface. You'd send a question, go do other work, and get a thoughtful response back later… like corresponding with a brilliant but busy colleague rather than talking to an always-on assistant.
This is a real tradeoff, not a temporary inconvenience. Fast, capable, private… pick two. Today's closed-source frontier models give you fast and capable. Tomorrow's open-source models gives you capable and private. No current technology, at a price activists can afford, gives you all three.
Currently, I think the right strategy is to build for both paths simultaneously. Use Path One now, with maximum privacy safeguards, because organizers need working tools today and cannot wait for the open-source ecosystem to catch up. Build toward Path Two so that when the hardware costs drop and the open models improve—and they will—the infrastructure is ready. Design every piece of OutcryOS so that swapping the AI backend from a cloud API to a local TEE-hosted model requires changing a configuration, not rebuilding the system.
AI activism is at a crossroads. The tools are powerful enough to matter. The infrastructure to run them privately doesn't yet exist at the quality and cost that activists deserve. I'm building the OS layer so that when it does, the transition is ready. In the meantime, I'll be honest about what's private and what isn't, and I work to shrink the gap every day.
OutcryOS is one attempt at an Activist Operating System. There should be others. The need is too large and too urgent for any single project to answer. But the premise is simple: organizers deserve an operating system built for the actual conditions of their work. An operating system. Encrypted at rest. Networked peer-to-peer. Intelligent by default. And under the control of the people who use it.
That's what we're building. Come see if it holds up.
OutcryOS: https://www.outcryai.com/os
Outcry API: https://www.outcryai.com/developer